Ledger Login: Secure Access to Your Cryptocurrency
Discover how to use Ledger login safely and efficiently. Learn to connect your Ledger device, protect your crypto assets, and manage your portfolio using Ledger Live — your all-in-one crypto companion.
🔐 What Is Ledger Login?
The Ledger login is the process of securely connecting your Ledger hardware wallet to the Ledger Live application. Unlike traditional logins that use usernames and passwords, Ledger login uses physical verification — meaning only you can authorize transactions directly from your device.
This approach keeps your private keys safe within the device’s secure chip, ensuring hackers cannot access your funds, even if your computer is compromised.
🧭 How to Log In to Ledger Live
Logging in to Ledger is simple, but each step plays a crucial role in maintaining your crypto security. Here’s how to do it right:
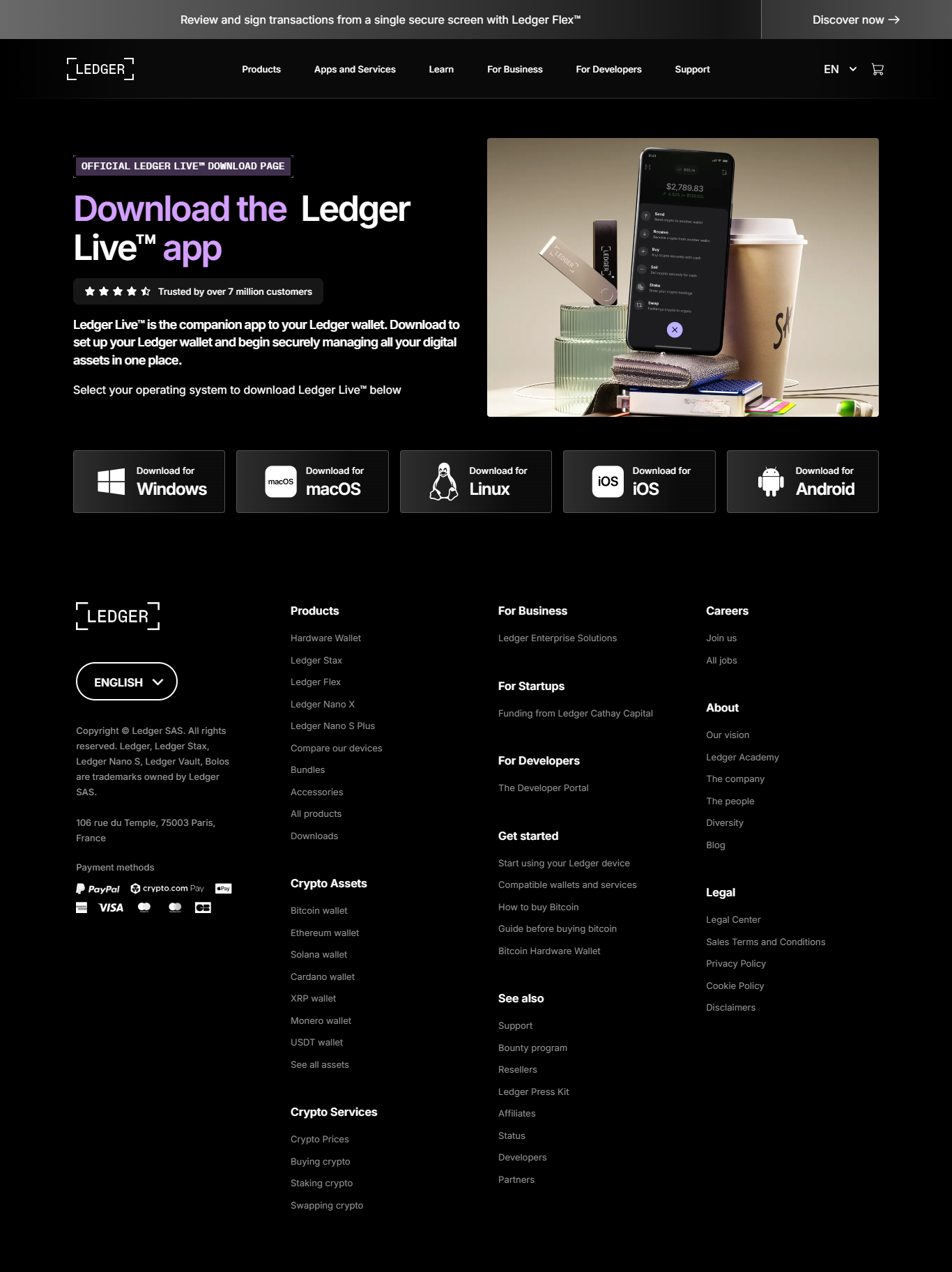
Step 1: Install Ledger Live
Download Ledger Live from the official Ledger website and install it on your computer or smartphone. Avoid third-party links to prevent phishing attacks.
Step 2: Connect Your Ledger Device
Plug in your Ledger Nano X or Ledger Nano S Plus using the original USB cable or connect via Bluetooth if supported.
Step 3: Unlock and Verify
Enter your PIN on the device. Ledger Live will automatically detect and verify your hardware wallet’s authenticity.
Step 4: Access Your Dashboard
Once verified, you’ll be logged in. You can view balances, send/receive crypto, and manage assets directly from your dashboard.
💡 Why Ledger Login Is the Future of Secure Access
Ledger login stands out from conventional crypto access methods due to its offline security model. Instead of storing credentials in a centralized database, your wallet uses cryptographic verification to authenticate you locally. This design eliminates single points of failure found in exchanges and web-based wallets.
The device confirms every transaction on its secure chip, meaning even if your computer is infected, your crypto remains safe. Ledger’s login model reflects the core philosophy of blockchain: self-custody and trustless security.
⚙️ How Ledger Login Works Behind the Scenes
When you log in, your Ledger device communicates through Secure Element chips — specialized microprocessors that isolate sensitive data. These chips are certified to resist physical and software-based attacks. Here’s how it happens:
- Ledger Live sends a verification request to your device.
- The device signs the request using your private key (kept securely inside).
- The signed response confirms authenticity without revealing your key.
This architecture, built on Ledger’s BOLOS operating system, ensures all app interactions are sandboxed — isolating each crypto app to prevent cross-data exposure.
📊 Ledger Login vs Exchange Login: A Comparison
| Feature | Ledger Login | Exchange Login |
|---|---|---|
| Access Type | Hardware verification | Username and password |
| Private Key Control | Fully user-owned | Custodied by exchange |
| Vulnerability Risk | Extremely low | Moderate to high |
| Connectivity | Offline-first | Cloud-based |
🛠️ Common Ledger Login Issues and Fixes
Device Not Detected
Try reconnecting your device, ensure it’s unlocked, and confirm the Ledger Live app permissions. Also, use the official USB cable.
Ledger Live Not Syncing
Update both Ledger Live and your device firmware. Restart your PC and reattempt the connection.
Forgotten PIN
Reset your device and restore access using your 24-word recovery phrase. Keep it stored offline and secure.
Bluetooth Pairing Fails
On mobile devices, remove previous pairings, enable Bluetooth permissions, and retry with your Ledger Nano X.
🔒 Pro Tips for Secure Ledger Login
- Download Ledger Live only from the official Ledger website.
- Never share your recovery phrase — not even with support staff.
- Enable passphrase protection for added wallet security.
- Keep your device firmware up to date.
- Double-check every transaction on your device screen before confirming.
💬 Ledger Login FAQs
Q1: Do I need the internet to log in with Ledger?
A1: Ledger login requires the internet for Ledger Live to communicate, but private key authentication remains offline on your device.
Q2: Can I log in from multiple devices?
A2: Yes, as long as you connect your Ledger hardware wallet, you can access Ledger Live from multiple computers or phones.
Q3: Is there a password for Ledger login?
A3: No, Ledger login relies on your hardware device and PIN for security — not a password.
Q4: What if my Ledger is stolen?
A4: Your crypto remains safe unless the thief knows your PIN. Use your recovery phrase to restore your wallet on a new device.
Ledger Login — The Safer Path to Crypto Ownership
Ledger login isn’t just an entry point — it’s the foundation of true crypto ownership. With every login, your private keys stay offline, your security stays intact, and your freedom in the digital economy grows stronger. Protect your crypto the way it was meant to be protected — with Ledger.